https://www.schneier.com/blog/archives/2017/07/australia_consi.html#comments I’ll be writing more on this in the coming days. I honestly hope this is not how it plays out.
Read more
Get help with Linux, Automation, Cybersecurity and more. AGIX staff have the know-how and experience to help your organisation with best-practices, current technology in various Cloud environments including Amazon AWS. Our technicians support Ubuntu, Redhat, Databases, Firewalls, Ansible and Terraform, Storage and more.
This page shows examples of our work that AGIX shares freely with you. For a fully supported compute environment, contact our team to find out how we can help your organization move forward in the right way.
Contact our friendly team to get started.

https://www.schneier.com/blog/archives/2017/07/australia_consi.html#comments I’ll be writing more on this in the coming days. I honestly hope this is not how it plays out.
Read more
In this article, I am arguing that a regulated Information Technology industry will result in higher quality systems and software and a new focus on security. Australia is about to create a new cyber warfare division within the Australian Defence Force. Whilst the details are still secret, the objectives will
Read more
This article covers server backups and guides you through the process of designing a backup plan. The process will result in a data backup plan that the business is comfortable with. How much data and time can your business lose without damaging your reputation and income? When a disaster hits,
Read more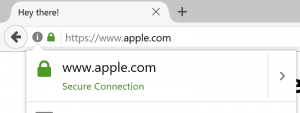
Think SSL protects websites? Think again. Check out this article and proof-of-concept “https://www.xudongz.com/blog/2017/idn-phishing/”. Try it yourself. Check out this article.
Read more
For those of you who follow my articles, you’d know that i’m a fan of the cloud. But more than that i’m a fan of using the right tool for the job. The decision on whether or not to use the cloud in your business should be an informed one.
Read more
It’s pretty simple to hide what you’re doing online. You’ve basically got two options, a) use a VPN, and b) use TOR. I’ll discuss both here. I’m simply sharing this information to answer questions. I’m not suggesting you use this for any dark reasons. Be good! The simplest way to
Read more
It’s completely silly to compare web browser power usage over anything short of hours of usage by people doing the same thing. In this short article i simply leave the browser windows open for a short period of time, idle, and using websites that i use daily. So yes, this
Read more
For times when standard broadband isn’t available, 4G may be a viable short term solution. This article notes what you need in order to get your service working. In this article we’ve used the TP-Link TL-MR6400 4G router. It has no ADSL capability. It has 4 ethernet ports, supports 802.11n
Read moreGoogle puts offline settings all over the place. It would be nice if there was a button in the G-Doc interface somewhere that said “Enable offline more for my documents” but sadly there isn’t. But it’s not hard to enable. Here’s how: In this example, i’ve used “example.com” as my
Read moreThis article explains how to migrate your Moodle to Enterprise LMS. My objective here is to migrate the entire Moodle including theme, plugins, users and course data from my Moodle to eLMS. I need SSH (command line) access to my Moodle for this to work because i need to backup
Read more